Sleep easy with Darktrace PREVENT
By introducing PREVENT into our ecosystem, it’s allowed us to identify assets that we previously thought business units had retired. PREVENT allows me to go home at the end of the day knowing my network, my users, the identity of my users, and my ecosystem are in good hands.

Klint Price
President of IT Operations and Cyber Security
Act first to
preempt threats.
Stay ahead of attackers with Darktrace PREVENT.
Hardens security proactively
Identifies and prioritizes risks
Conducts continuous around-the-clock testing
Emulates attacks to test vulnerabilities
Makes attacks more costly for attackers
Darktrace
PREVENT
™
/
Attack Surface Management
Continuously monitors your attack surface for risks, high-impact vulnerabilities and external threats.
Unparalleled Discovery
Darktrace PREVENT/ASM uses AI to understand what makes an external asset yours, searching beyond known servers, networks, and IPs, typically surfacing 30% - 50% more assets than an organization realizes it has.


Actionable Insights
Provides a high-level overview of the evolution of your attack surface and associated risks. Presents trends on key metrics such as the type of risks found and their criticality for prioritization.
Hardening Systems
Darktrace PREVENT communicates findings to Darktrace DETECT + RESPOND to harden protections around critical chokepoints.

Darktrace
PREVENT
™
/
End-to-End
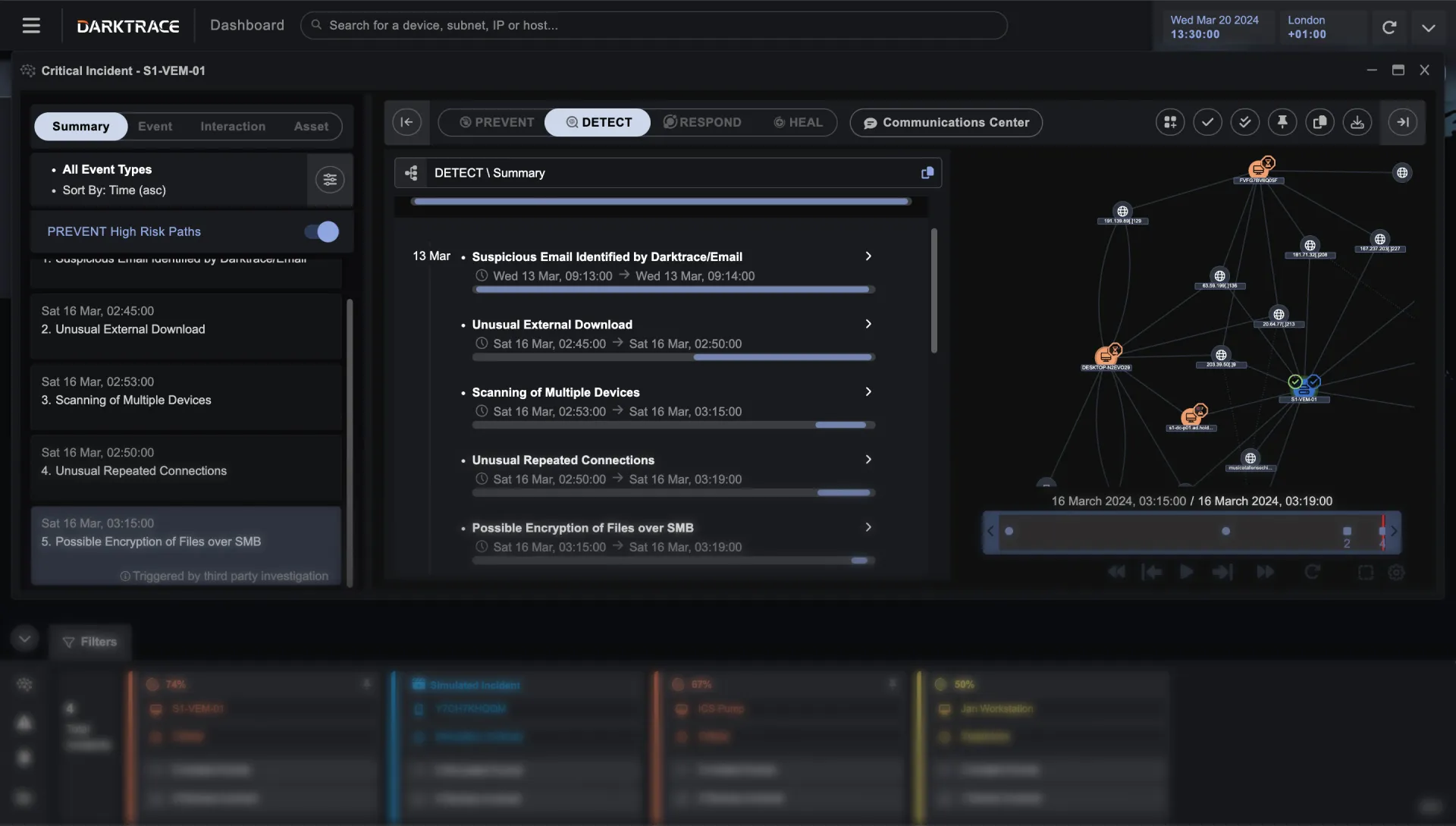
Proactively prevents cyber-attacks before they occur. Identifies and prioritizes high-value targets and pathways to secure vital internal systems and assets.
Attack Path Modeling
Map the most relevant and impactful attack paths through your organization in real-time with this revolutionary approach. Darktrace/E2E delivers continuous visibility into the most vulnerable – and valuable – paths everywhere your data sits.


Pentest Augmentation
Darktrace/E2E continuously identifies all potential pathways and analyzes every digital touchpoint.
View organization from attacker's perspective
Model scenarios: How would an attacker get to a key asset?
Assess potential damage
Allocate resources based on prioritized pathways
Automate a labor-intensive process
Identify at-risk and exposed user groups
Breach & Attack Emulation
Identified critical attack paths allow Darktrace/E2E to engage via AI-generated social engineering, which closely align with real-world attack scenarios.


Security & Awareness Training
Identify users who are exposed or potentially vulnerable to phishing, allowing IT teams to tailor training based on real-world data. Darktrace/E2E mimics the best attackers to test human defenses and incident response processes.
Cyber Risk Prioritization
Darktrace/E2E prioritizes vulnerabilities - complete with suggestions about how to harden them. Combined with Darktrace DETECT + RESPOND, it autonomously implements countermeasures to ensure your critical vulnerabilities and attack paths can’t be exploited and cause damage.

Darktrace ActiveAI Security Platform
The Active AI Security Platform correlates threats across your entire organization, delivering proactive cyber resilience with real-time detection and autonomous response to known and novel threats.
더 알아보기